Meta adds proof-based security to encrypted backups
May 5, 2026
Meta has updated its infrastructure for protecting password-based and end-to-end encrypted backups, introducing over-the-air fleet key distribution for Messenger and a commitment to publishing evidence of secure fleet deployments.
How encrypted backups work
These updates build on the company’s HSM-based Backup Key Vault, which provides end-to-end encrypted backups for WhatsApp and Messenger. The system protects users’ backed-up message history with a recovery code stored in tamper-resistant hardware security modules (HSMs) that are inaccessible to Meta, cloud storage providers, or third parties. The vault operates as a geographically distributed fleet across multiple data centers and uses majority-consensus replication for resilience.
Meta has offered end-to-end encrypted messaging since 2016, while backups stored in cloud services did not receive the same level of protection. The updated system strengthens this model by ensuring that only users can decrypt stored data.
When end-to-end encrypted backups are enabled in WhatsApp, the client generates a unique 256-bit encryption key using a built-in cryptographically secure pseudorandom number generator. The key remains on the client and is never transmitted unencrypted.
Decrypting a backup requires this key. The client encrypts and registers the key material with WhatsApp, creating a record in the HSM-based Backup Key Vault tied to the device. This process uses the OPAQUE protocol, allowing the key to be stored with a password without revealing the password to the vault. The key can be retrieved only if the user proves knowledge of the password, ensuring that only the user can access and decrypt the backup.
Over-the-air key distribution
Users validate the HSM fleet’s public key to confirm authenticity before establishing a session. In WhatsApp, these keys are hardcoded. For Messenger, Meta distributes fleet public keys over the air as part of the HSM response. They are delivered in a validation bundle signed by Cloudflare and counter-signed by Meta, providing independent cryptographic proof of authenticity. Cloudflare also maintains an audit log of these bundles.
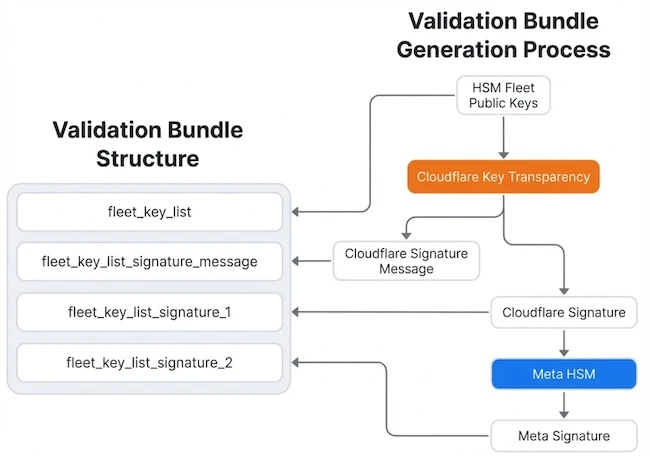
Over-the-air key distribution (Source: Meta)
Deployment verification and transparency
Meta will publish evidence of the secure deployment of each new HSM fleet, allowing users to verify deployments by following the steps in the Audit section of the Security of End-To-End Encrypted Backups whitepaper.
“Transparency in the deployment of our HSM fleet is essential to demonstrating that the system operates as designed and that Meta cannot access users’ encrypted backups,” the company said.
Meta also provides the open-source mbt CLI for independently verifying artifacts in its binary transparency log. It uses Cloudflare’s Ed25519 public key as a trust anchor and validates SHA-256 digests, signatures, and consistency against Cloudflare’s Key Transparency auditor.
Search
RECENT PRESS RELEASES
Related Post



